Case Study: Singhealth Data Breach Cyber Attack with Timelines
OVERVIEW
Between June 27 and July 4 2017, a foreign, persistent and sophisticated threat group broke into SingHealth’s system and gained access to the Sunrise Clinical Manager (SCM) database holding electronic medical records. It stole the personal data of 1.5 million patients and the outpatient medication records of 160,000 of them — including Prime Minister Lee Hsien Loong’s. It was categorised as an advanced persistent threat (APT) attack.

Years and Incidents as follow:
2014
Untrained staff in the Cancer service registry and development ended up managing SCM server due to “convenience” as server was located at NCCS. Said-manager was given login credentials even though he was not authorised on paper to be in charge of managing the server. Original staff overseeing management of server left and no one took over the management of server.
2017
Server had not received necessary security software for more than a year.
May 2017
Server was unable to update WannaCry antivirus software as it was too old and had to be disconnected from the SingHealth network before manual antivirus software installation and virus signature updates could be performed.
May – June 2017
Failed, but undetected, attempts to seek out Electronic Medical Records (EMR) records by exploiting inactive administrative accounts to remotely log into server linked to EMR.
August 2017
User in Singapore General Hospital (SGH) fell to phishing attack
13 June 2018
Attempts of breaches were identified and cybersecurity staff were looped in about breaches.
18 June
Supervisor finally read emails about incident after being away on leave till June 17.
18 - 27 June
Inaction by staff despite emails about incident.
27 June - 4 July
Multiple attempts were made to access SingHealth’s EMC. Queries were made, but management was misinformed that there were no results.
July 4
Attempts were detected and terminated by database administrator, attack was halted, but this was not reported to upper management.
July 9
Query was made, but management was misinformed that there were no results.
July 10
Upper management redid a query to “double check” and detected that personal data and medical records were stolen. Cyber Security Agency, Ministry of Health and SingHealth were informed of the cyber attack
July 20
Singaporeans were informed of the cyber attack
ISSUES
Signs of an attack were observed, but they were not acted upon because of the relevant employees’ inability to recognise that an attack was ongoing, and inaction on the part of staff members responsible for responding to attacks. There was a fundamental lack cyber-security awareness and inadequate training to understand the severity of the attack and to respond effectively to the attack. Had appropriate and timely action been taken, the attacker could have been stopped.
Vulnerabilities and weaknesses in the SingHealth’s network and SCM system contributed to the attacker’s success in obtaining data.
The SCM database, which is legally owned by SingHealth, functioned on an open network that was linked to the Citrix servers of SGH, a vulnerability the hacker exploited.
There was a lack of monitoring of the SCM database for unusual queries and access and no existing control to detect or block bulk queries being made to the database. Also, the Citrix servers of SGH were not monitored for real-time analysis and alerts of vulnerabilities and were not adequately secured against unauthorised access.
The process requiring 2-factor authentication (2FA) for administrator access was not enforced as the exclusive means of logging in as an administrator. This allowed the attacker to access the server through other routes that did not require 2FA. There was also the issue of weak administrator account passwords which may have been exploited by the hacker.
The attacker was skilled, patient and persistent and demonstrated network intrusion techniques with low attack signature These are hallmarks of an advanced threat actor. The attacker was able to evade detection for almost ten months from August 2017, was conscientious in erasing logs on compromised workstations and servers, and even re-entered the network after being detected to erase system and programme logs. However, he was “stealthy but not silent” and left traces that could have been detected, had human lapses not occurred.
RECOMMENDATIONS
Cultural changes within the organisation. Design a proper chain of command and specialized roles overseeing cyber security. Improve the work culture concerning cyber security so that relevant employees have a sense of urgency and responsibility to protect the system from threats.
Enhance cyber-security awareness among all employees, increase capacity to prevent, detect and respond to security incidents. Train employees on secure authentication, how to better identify social engineering attacks, handling sensitive data, how to deal with unintentional data exposure, and identifying and reporting incidents.
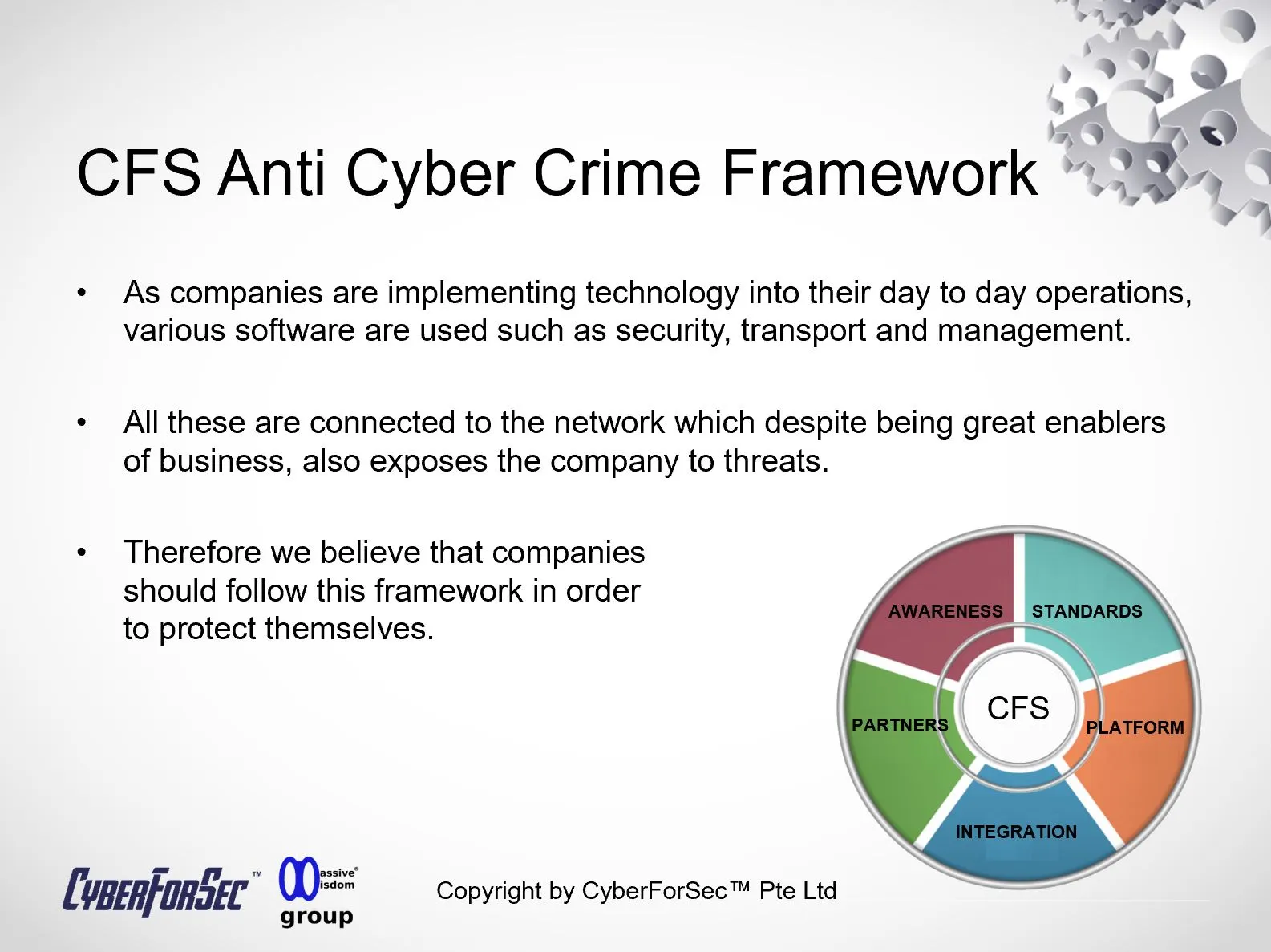
Concrete cybersecurity defence. Improve cyber stack (the layers of security technology that an organisation puts in place to form an integrated defence to cyberattacks). Provide advanced endpoint security solutions. Review effectiveness of endpoint security measures.
Conduct code review of applications that are installed on critical systems and ensure that such reviews have been performed to their satisfaction. Verify that there are no instances of insecure programming or security flaws that may present vulnerabilities or backdoors that could be exploited by cyber attackers.
Subject privileged administrator accounts to tighter control and greater monitoring. All administrators are to use 2FA when performing administrative tasks. Centrally manage server local administrator accounts across the IT network.
Education of the people, by educating the administrators and team to carry out auditing in order to equip themselves with the latest security protocols and software to deter any threats. On top of that the people handling the systems have to be sufficiently educated to handle the required software.
- Cyber-security exercises
Conduct vulnerability audits and tests to check on defence and security of systems. Case in point where the Government invited hackers to try to hack into their systems.
Design incident response plans and test them out via conducting real life simulation breaches, which are similar to emergency exercises. These simulation exercises should involve the entire organisation, across all ranks including senior management and directors. Incident response plans are to be reviewed after every simulation exercise.
Carry out penetration testing and red teaming (a group of white-hat hackers attack an organisation’s digital infrastructure to test the organisation’s defence) regularly. Consider carrying out threat hunting to seek out potential attackers.
- Industry
Create an ecosystem of sufficiently trained security professionals to mitigate threats in a timely and appropriate manner.MOVING FORWARD
Singapore is vulnerable to attacks such as cyber-terrorism, cyber-espionage and politically-charged cyberattacks. The Government holds cradle to grave data and governmental agencies will always targets. There has been 4 data breaches in a short span of two years . This does not bode well for Singapore in meeting her goal of a Smart Nation by 2023 where citizens would be able to complete 90-95% of transactions with the government digitally. A thorough cybersecurity review across all government agencies has to be conducted.
On the bright side, there is an awareness of the importance of cyber security as evident in the passing of the Cyber Security Act in March 2018 and there is representation in the Cabinet by the Minister of Communications and Information S. Iswaran, acting as the Minister in Charge of Cyber Security. Ministries are not resting on their laurels too, with the Maritime and Port Authority establishing a Maritime Cybersecurity Operations Centre in November 2018 to monitor cyber threats against CIIs and creating a network of ports in Asia and Europe to exchange of information on cybersecurity issues.
However more needs to be done outside of the political front, there needs to be a fundamental cultural and mindset change within public and private organisations. They will have to understand the importance and urgency of cybersecurity. It is also critical to clarify the many misconceptions about cybersecurity and the specialised job scope its staff does.
In April 2017, four Singapore universities were victims of online attacks, with at least 52 online accounts breached to obtain research articles without authorisation. In April 2017, National University of Singapore and Nanyang Technological University were hit by IT network breaches. In 2017, the Ministry of Defence revealed its I-net system was attacked and the personal data of 850 national servicemen and employees was stolen.
References / Sources:
- SingHealth cyber attack: How it unfolded | The Straits Times: This is an interactive graphic that shows the timeline and details of the cyber attack, as well as the actions taken by the authorities to contain and investigate the incident.
- Hacker group behind SingHealth data breach identified, targeted mainly Singapore firms | ZDNET: This is an article that reveals the identity and motives of the hacker group, dubbed Whitefly, that was responsible for the cyber attack. It also describes the methods and tools used by the hackers, as well as the impact and implications of the breach.
- SingHealth Data Breach: A Series of Unfortunate Cybersecurity Events | Packetlabs: This is a blog post that provides a technical analysis of the cyber attack, including the vulnerabilities exploited, the malware deployed, and the data exfiltrated. It also offers some recommendations and best practices for improving cybersecurity posture and resilience.
- Firms fined $1M for SingHealth data security breach | ZDNET: This is an article that reports on the financial penalties imposed by the Personal Data Protection Commission (PDPC) on SingHealth and IHIS for failing to protect the personal data of patients. It also outlines the measures taken by both entities to prevent future breaches.
By Alvin Lam Wee Wah
and Team at CyberForSec.
Interested in what you've read and want to know more or collaborate with us? Contact us at customersuccess[a]cyberforsec.com replacing the [a] with @.