Demystifying Email Phishing: Your Guide to Prevention
In today's digital age, email has become an indispensable tool for communication, both in our personal and professional lives. However, with its widespread use, email has also become a prime target for cybercriminals who employ a tactic known as "email phishing" to deceive individuals and organizations. In our latest CyberForSec blog post, we delve into the intricacies of email phishing, how it works, and, most importantly, how you can protect yourself from falling victim to these malicious schemes.

Understanding Email Phishing
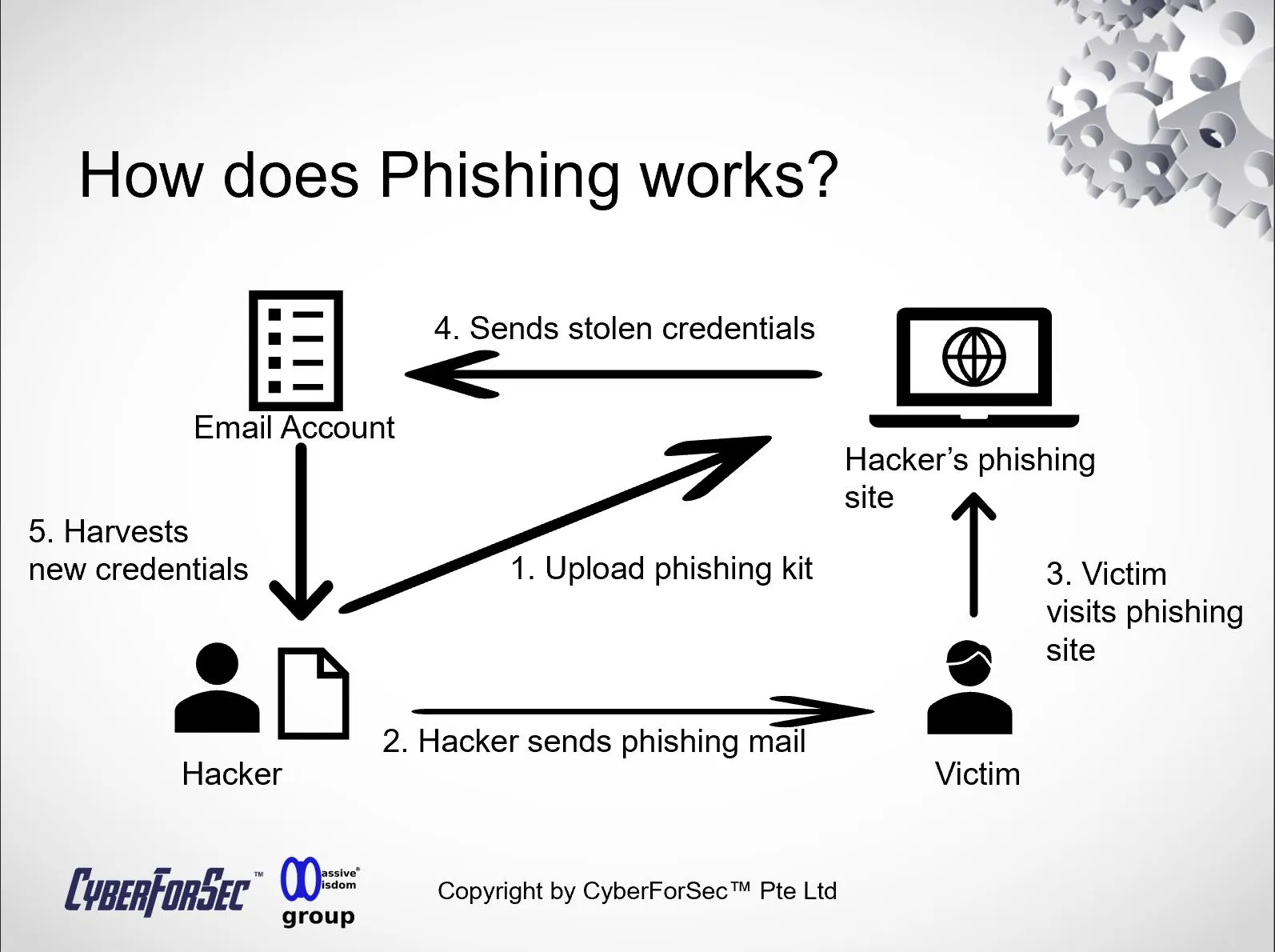
Email phishing is a cyberattack technique that relies on deception and manipulation to steal sensitive information, such as login credentials, financial data, or personal details. Here's how it typically works:
- Deceptive Emails: Phishers craft emails that appear to come from legitimate sources, often mimicking trusted organizations, colleagues, or government entities. These emails are carefully designed to look convincing, complete with logos, branding, and even official language.
- Urgent or Tempting Content: Phishing emails often contain urgent or enticing content to provoke quick action. This could be a fake invoice, a security alert, a prize notification, or a request for sensitive information.
- Malicious Links or Attachments: Within the email, there are usually links or attachments that, when clicked or opened, lead to malicious websites or trigger the download of malware onto your device.
- Social Engineering: Phishers employ psychological manipulation tactics to create a sense of urgency, fear, or curiosity, compelling recipients to take the desired action without thinking.
Preventing Email Phishing Attacks
Now that you have a clearer understanding of how email phishing works, let's explore the most effective strategies to shield yourself from these fraudulent attempts:
- Verify Sender Authenticity: Always double-check the sender's email address. Hover over links to preview the URL destination. If anything seems suspicious, contact the sender directly through official channels to confirm the email's legitimacy.
- Be Skeptical: Question the urgency and legitimacy of unexpected emails, especially those requesting sensitive information or payment. Phishing emails often pressure recipients to act hastily.
- Avoid Clicking Unverified Links: Hover over links without clicking to see where they lead. If you receive an email urging you to click a link, verify its authenticity independently before taking any action.
- Don't Download Suspicious Attachments: Refrain from downloading attachments from unknown or unverified sources. Cybercriminals often use malicious attachments to infect your device with malware.
- Use Email Security Software: Employ robust email security software that can detect and filter out phishing emails. Such tools are designed to recognize common phishing patterns and protect your inbox.
- Educate Yourself and Others: Stay informed about the latest phishing tactics and educate your colleagues or family members to recognize phishing attempts. Awareness is a powerful defense.
Stay One Step Ahead with CyberForSec
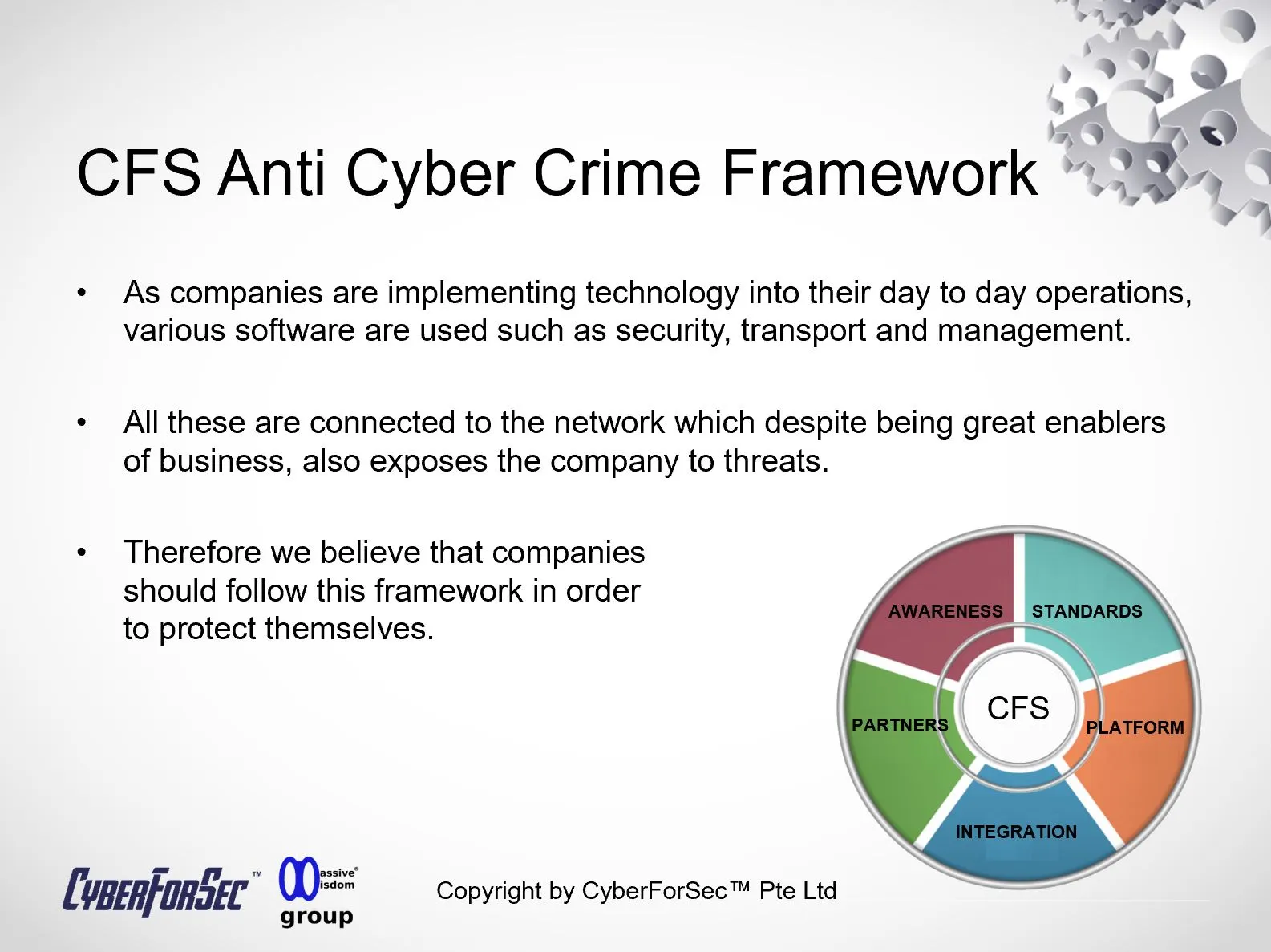
At CyberForSec, we believe that knowledge is the first line of defense against cyber threats. Our blog post on email phishing equips you with the understanding and tools to protect yourself and your organization from falling victim to these insidious attacks. Don't let cybercriminals compromise your security; take proactive steps to safeguard your digital world.
Stay tuned to CyberForSec's blog for more insightful articles on cybersecurity, emerging threats, and best practices for staying safe in the digital age. Your security is our priority.
By Alvin Lam Wee Wah
and Team at CyberForSec.
Interested in what you've read and want to know more or collaborate with us? Contact us at customersuccess[a]cyberforsec.com replacing the [a] with @.