New Growth Area Number 1: Cyber Security - Safeguarding the Digital Frontier
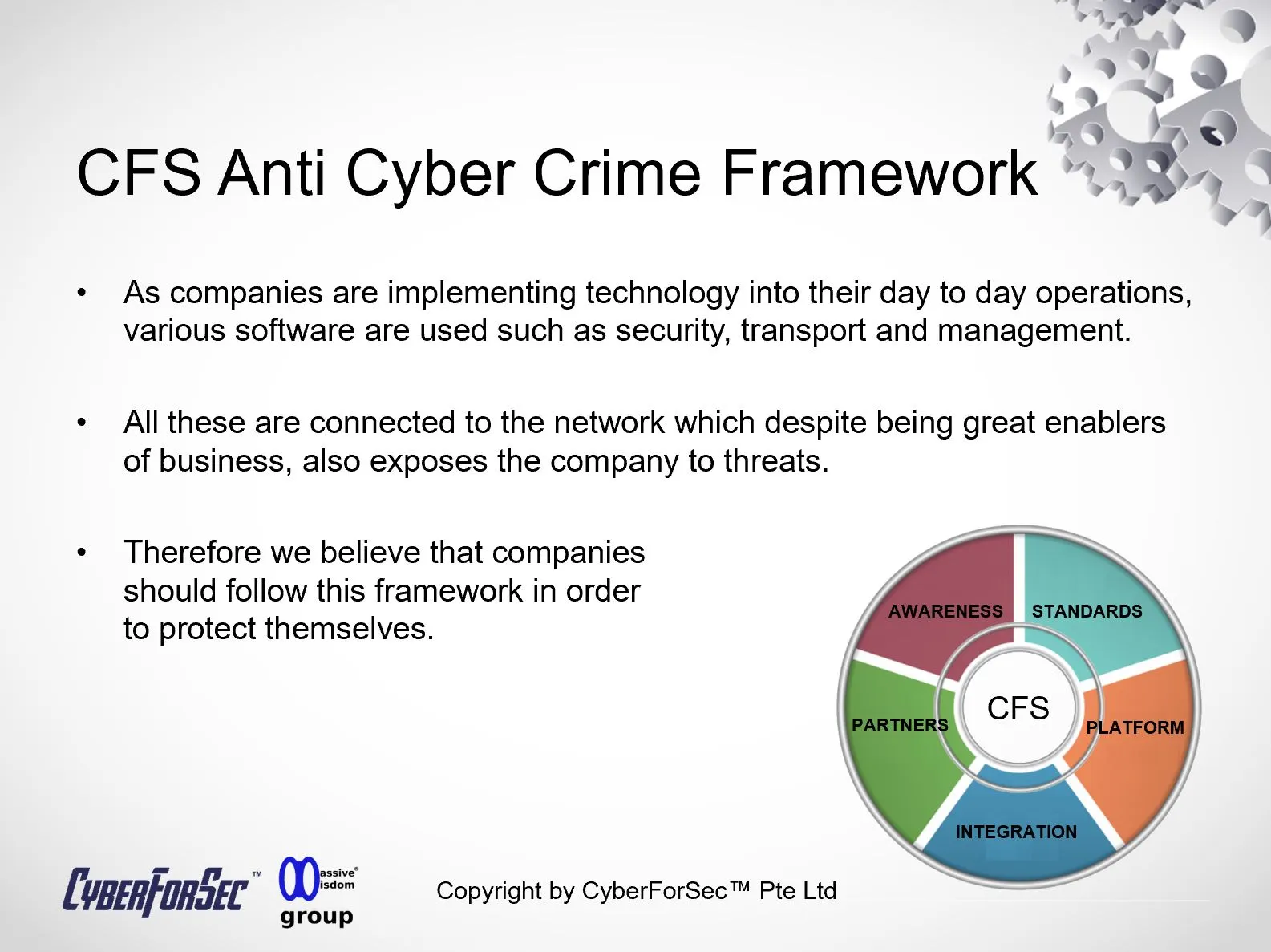
In an era defined by rapid technological advancement, businesses and organizations have become increasingly reliant on technology to store and manage their most sensitive and confidential data. While this digital transformation has ushered in unprecedented convenience and efficiency, it has also opened the door to a new breed of criminals: cyber attackers. These threat actors are drawn by the allure of valuable data and information, making cyber security a paramount concern for individuals, businesses, and governments worldwide.

One of the most notable incidents that underscored the urgency of robust cyber security measures was the Sony Email leak in 2014. This high-profile breach exposed a wealth of sensitive and confidential information, including executive emails, employee data, and unreleased films. The repercussions were not limited to Sony's reputation and financial losses but extended to diplomatic tensions between nations, as the attack was attributed to North Korea.
Another significant event that shook the corporate world was the Target credit card breach in 2013. In this case, cyber criminals infiltrated Target's payment system, compromising credit and debit card information of millions of customers. The fallout included substantial financial losses, damage to the company's brand, and increased scrutiny of cybersecurity practices across industries.
The lessons learned from these and other cyber attacks are clear: the digital landscape is fraught with risks, and organizations must take concerted efforts to protect their digital assets and confidential data.
Why Cyber Security Matters More Than Ever
As technology continues to evolve, so do the tactics and sophistication of cyber criminals. To counter this evolving threat, a collaborative approach between Cyber Forensics and Cyber Security experts is imperative. These experts work together to not only prevent and mitigate cyber attacks but also investigate and gather evidence when breaches occur.
Sources:
The Cyberforsec Blog delves deeper into the realm of cyber security, providing insights, best practices, and the latest trends to help individuals and organizations navigate the ever-changing cyber threat landscape. Join us as we explore the vital role of cyber security in safeguarding our digital future and the collaborative efforts required to stay one step ahead of cyber criminals. Together, we can build a more secure digital world.
By Alvin Lam Wee Wah
and Team at CyberForSec.
Interested in what you've read and want to know more or collaborate with us? Contact us at customersuccess[a]cyberforsec.com replacing the [a] with @.